
IBM PCjr zero-day data-destroy vulnerability (AKA: Joykill).
Description
This vulnerability allows local and remote attackers to destroy the contents of the floppy diskette. User interaction is required to exploit this vulnerability. The issue results from the lack of proper validation when starting the manufacturing system test.
Exploit (local)
- Plug the two joysticks into the IBM PCjr
- Insert diskette in floppy drive (data will get destroyed!)
- Press Ctrl + Alt + Ins. to enter into diagnostics mode
- Immediately after, press:
- Joystick 1 button B
- Joystick 2 buttons A + B
- Diskette data will get destroyed
Exploit (remote)
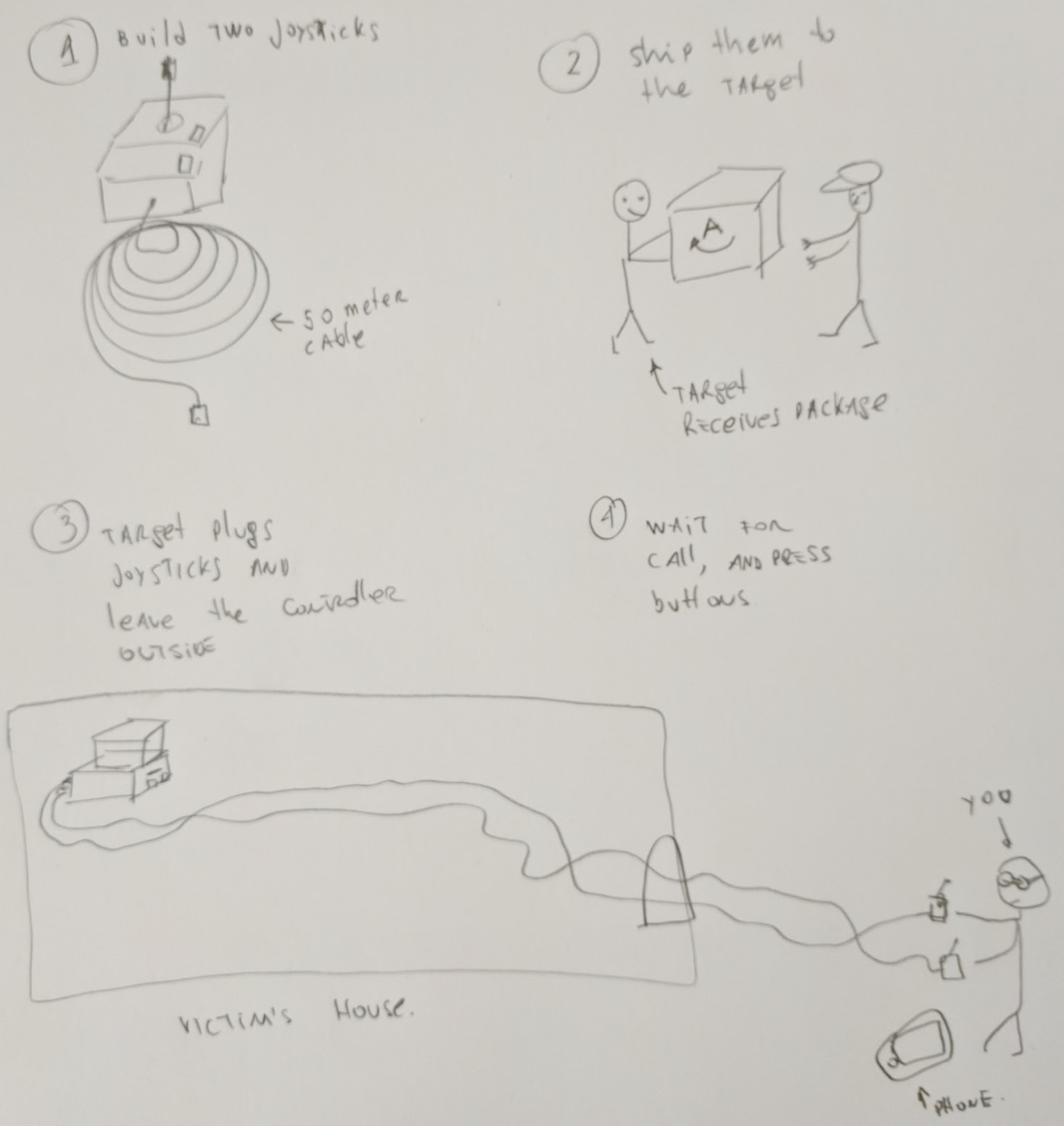
A step-by-step of how to remotely exploit the vulnerability.
- Build two IBM PCjr joysticks with 50-meter long cables
- Ship them to the target user with a letter saying:
Dear customer,
As a token of our gratitude, we are sending you these two joysticks that will let you do an online backup of your most valued diskettes.
Please, plug them in your PCjr, and leave the controllers outside your house. Call us at our support call-center {insert your phone number} once you are ready for the online backup.
Don’t forget to insert your most valued diskette in the floppy drive!
Yours,
IBM PCjr tech support.
- Wait until the user places the two joysticks outside his house and wait for his call. Once he/she calls you, press the joysticks buttons described above and respond with:
Thank you for calling IBM PCjr online backup service.
Please, press Ctrl+Alt+Ins in your PCjr to initiate the online backup service.
Ka-boom! The user data will get destroyed!
Responsibility disclosure
- Retro Moe called 1-800-222-PCjr multiple times. The person on the other end of the line seems to know nothing about the IBM PCjr computer. In fact, it seems that he/she knows nothing about IBM.
Technical description
IBM PCjr contains built-in diagnostics code in the ROM. This diagnostics code has undocumented features to perform the manufacturing and service tests:
- Manufacturing burn-in mode: All 4 buttons pressed
- Manufacturing system-test mode: All 4 buttons pressed except Joystick 1 button A
- Service loop-post mode: All buttons pressed except Joystick 1 button B
- Service system-test mode: All buttons pressed except Joystick 2 button A
When entering in “Manufacturing system-test mode”, all internal tests (diskette, video, joystick, sound, printer, modem) will be performed without user interaction. The first test, and without any warning, is the diskette test that will destroy the diskette data. Since there is no visual indication of what’s happening, port 0x10 will have the test number that is being executed.
Why IBM did this
Retro Moe strongly believes that IBM left the code undocumented on purpose to prevent people from performing their own in-depth diagnostics. That way IBM could charge you extra money for that.
Retro Moe knows that by disclosing this vulnerability many IBM PCjr Technical Support employees might lose their jobs (since they will no longer be needed). But Retro Moe also believes in Power to the people, and knowledge is power!
For more information, all the undocumented features, including a Joystick test performed with keyboards go:
About
Retro Moe does stuff related to joysticks (like the UniJoystiCle and this vulnerability) and some other stuff not related to joysticks at all.